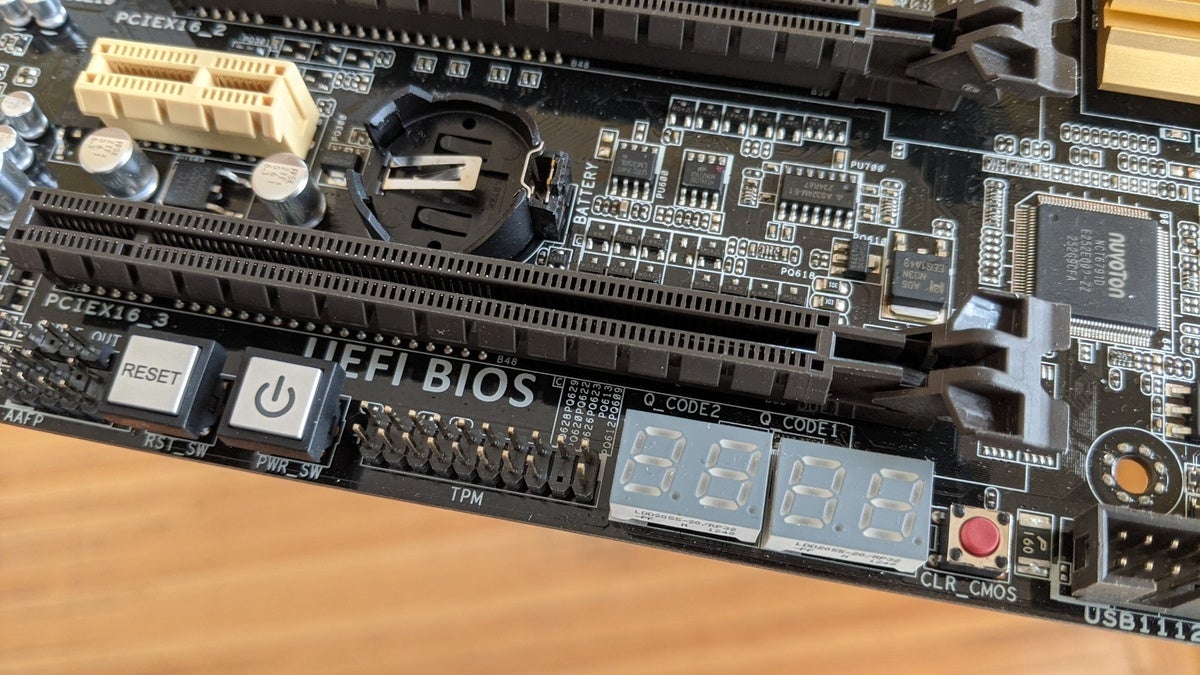
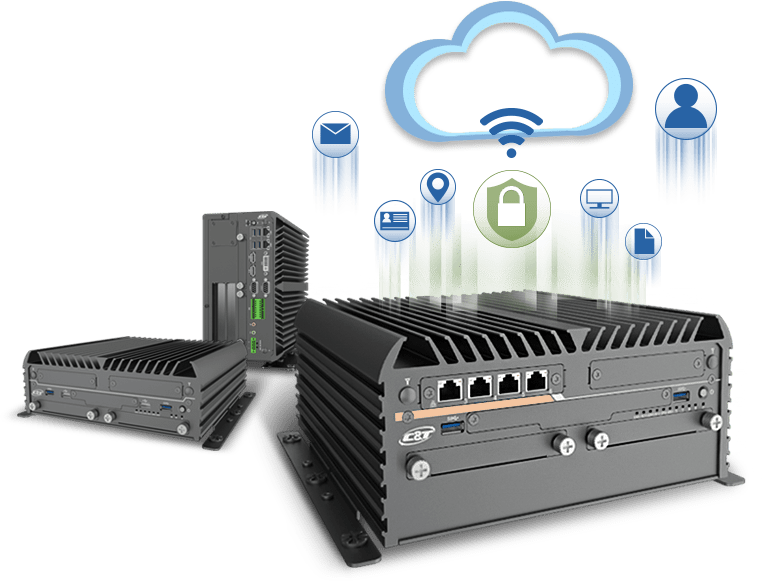
Using a trusted platform module and trusted brokered IO as the foundation of IoT security - Embedded Computing Design

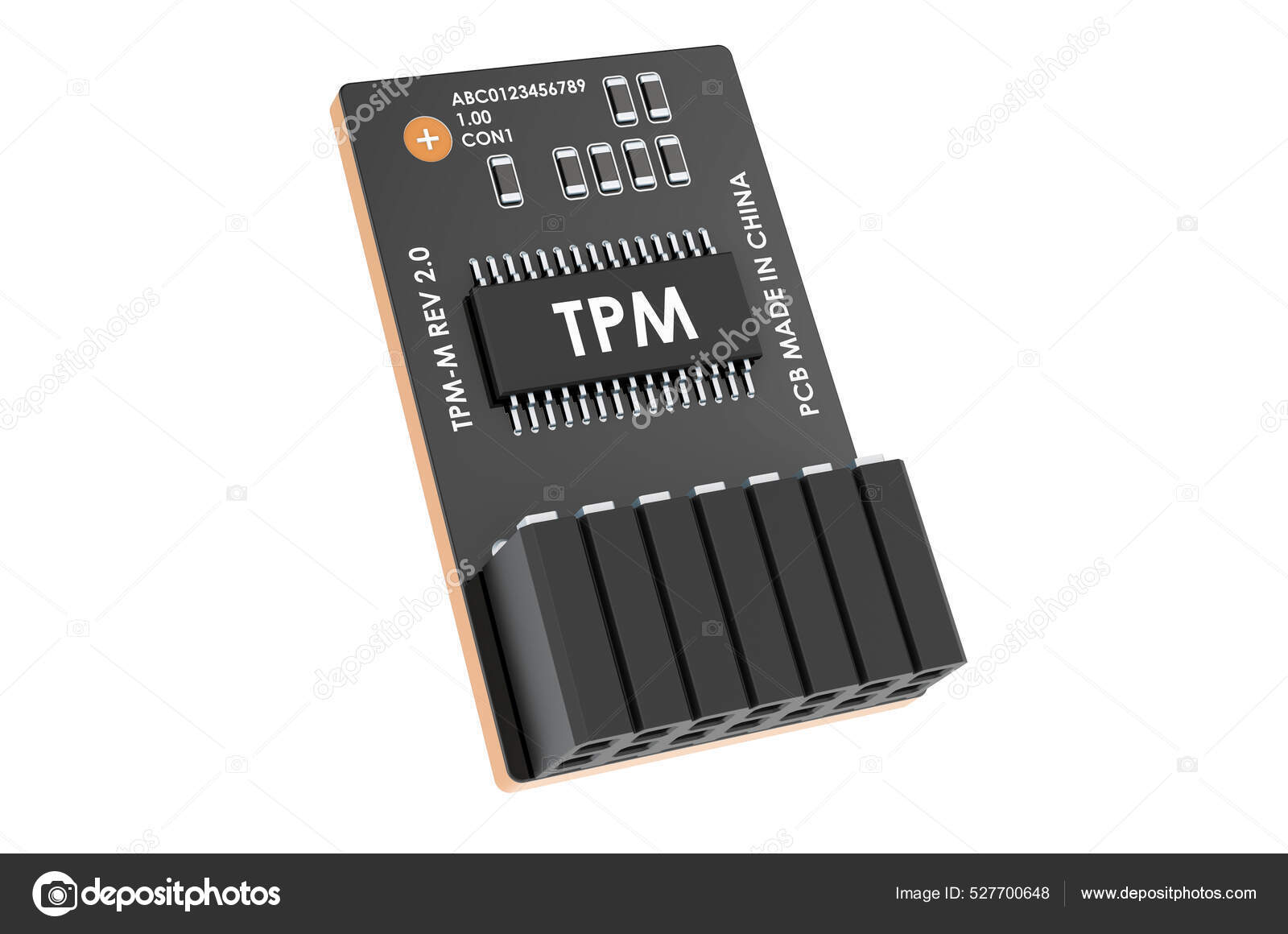
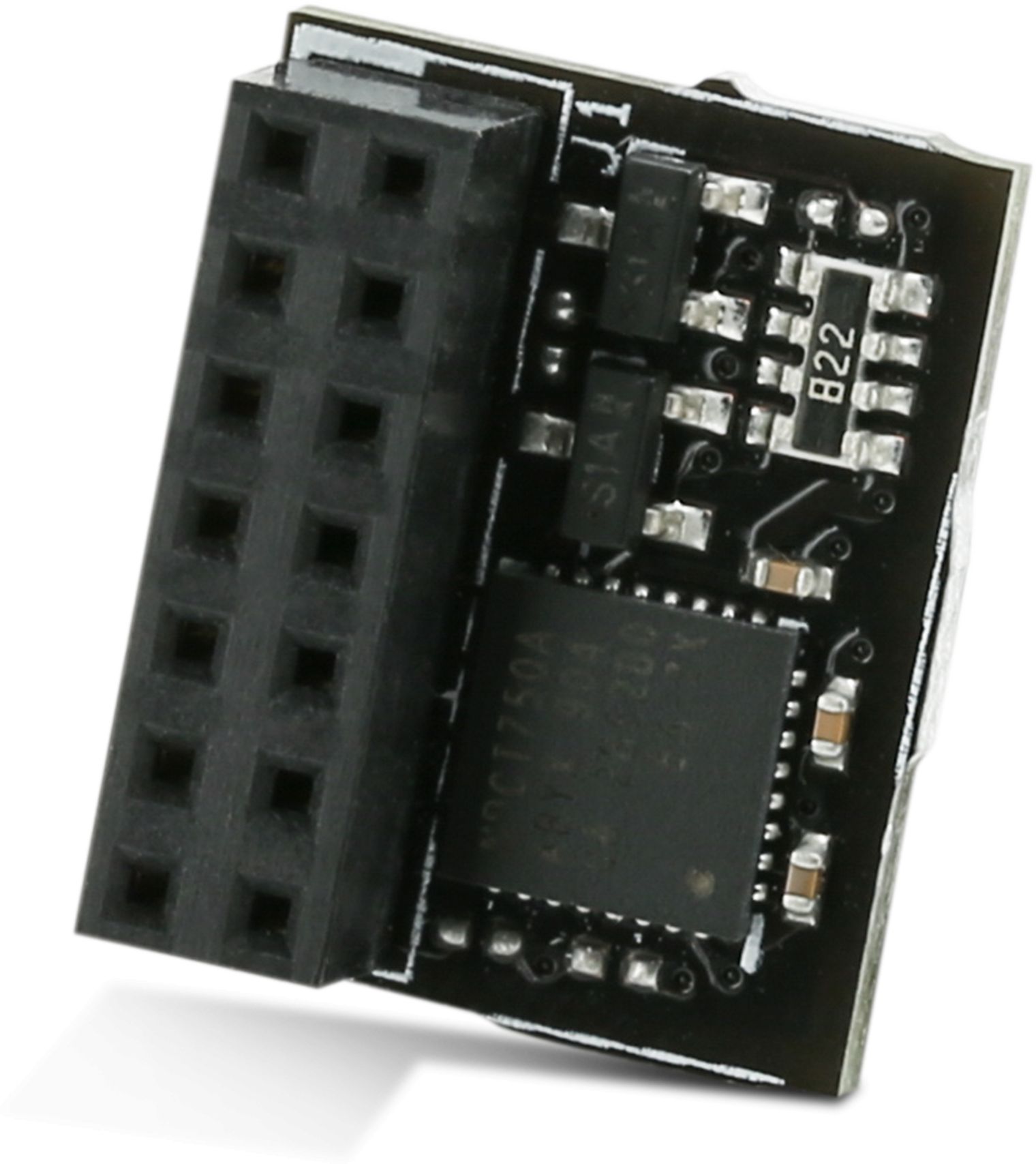
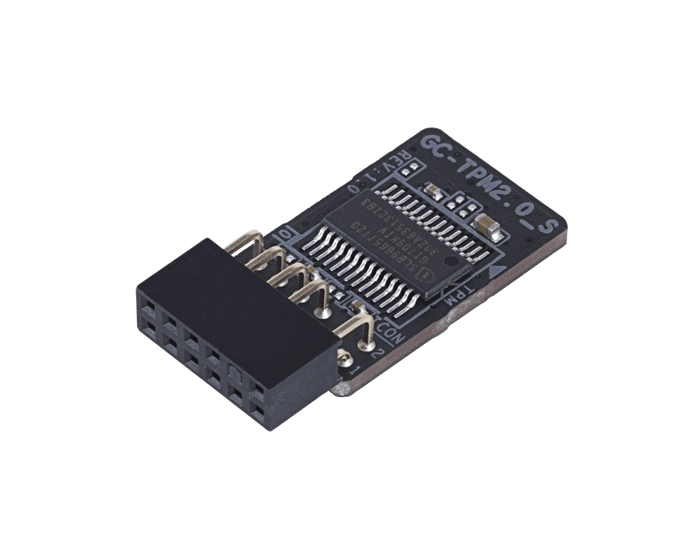
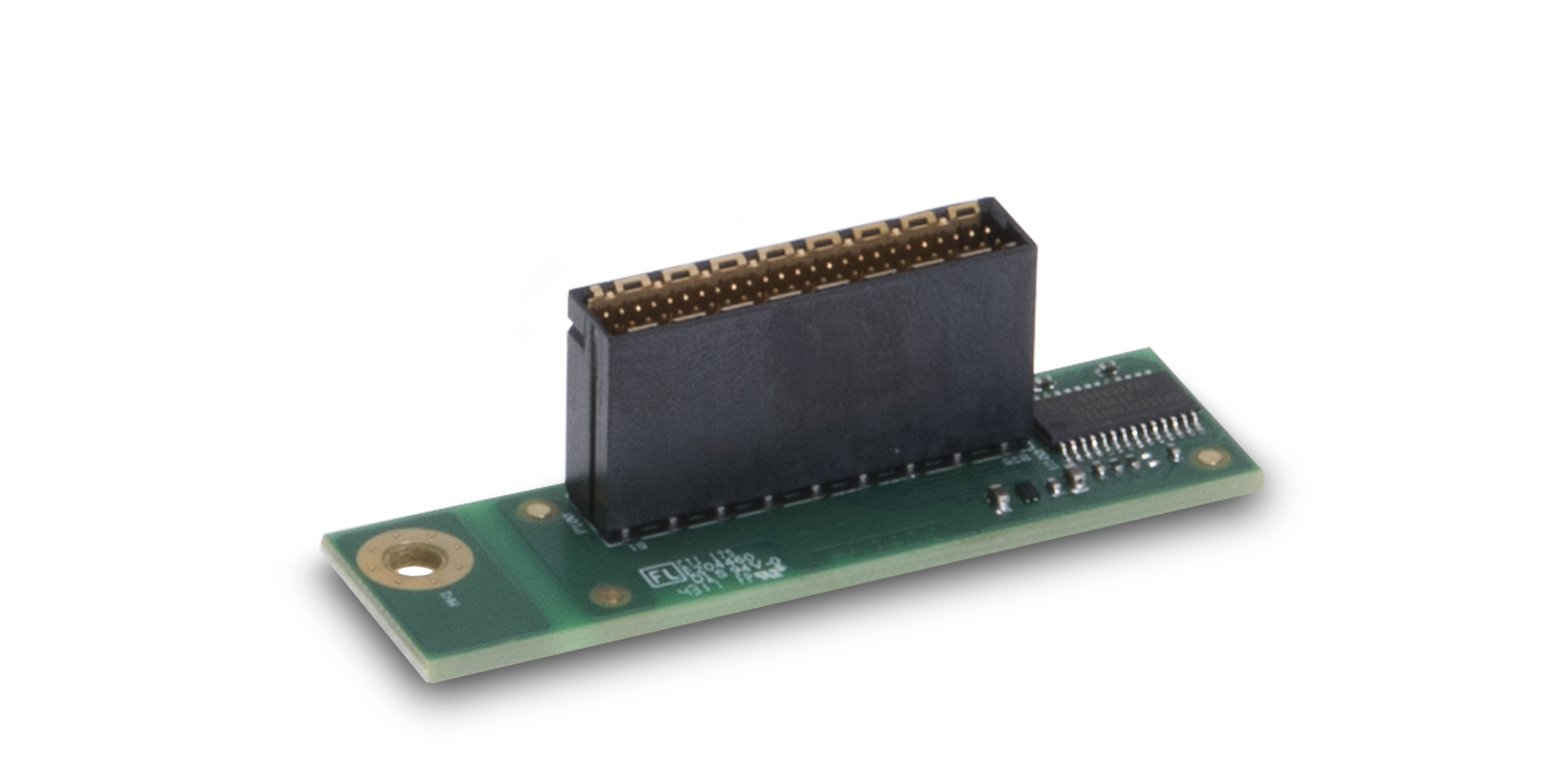
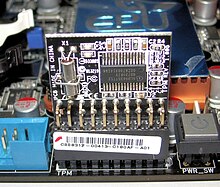
A Trusted Platform Module (TPM) consists of shielded locations (memory)... | Download Scientific Diagram

What is a Trusted Platform Module (TPM)? Protecting your PC and data through hardware encryption - YouTube